It goes without mentioning that the problem regarding identity theft is a grave one. If you check reports from the past, you will find millions of people falling prey to identity theft every year. However with the advancement in the knowledge of the hackers to steal your identity, the way they adopt are also becoming more and more advanced. Gone are those good old days when the thieves used simple ways of stealing personal details like rummaging through trash cans in ATM outlets and other data files.
Thieves have become more sophisticated and they’re using new gadgets to hack your financial information. We will take a quick look at the main gadgets which thieves use nowadays to deceive people.

#1: Skimmers
One of the most common ways in which the fraudsters and identity thieves capture all kinds of data on your debit card is through a process which is called skimming. There is a device for data storage which is attached to the ATM machine, though we may have heard such devices being used with credit card readers as well. The transaction will still work but simultaneously it will also make another digital copy of all your credit card information. This is why experts always recommend people not to leave your ATM card out of sight to avoid such hackings.
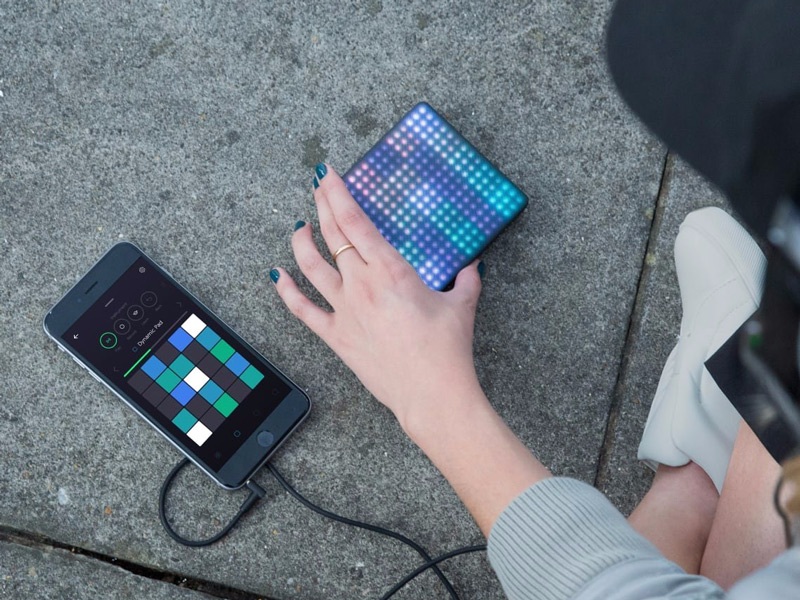
#2: RFID readers
One more way in which criminals steal information is through something that is called an RFID reader. There are tap-to-pay technologies which are built into few cards and through this the RFIC technology is used to transmit data. While hackers will require positioning the readers who are very close to you, the transfer of required information will be completed within few seconds. This is a machine which costs $300 and 7 among 10 tap-to-pay cards might be at great risk.
#3: Laptops
Though this might be a no-brainer because we all know that using laptops is necessary for all sorts of tasks yet it is seen that there are identity thieves who use their own laptops to receive access to the data, as per reports from Identity Theft Security. A thief usually drives through the locality and watches out for unsecured hotspots. Once the thief finds you out, it logs on to your wi-fi network and chooses to break into connected devices. You should henceforth make sure that the firewall of the computer is running properly. Don’t leave your wireless connection unsecured and choose a password that’s tough to crack.
#4: Your personal old gadgets
There is yet another point that many ignore. You may have gadgets which can work against you. Whenever we dispose of our old smartphones, we forget to ensure that all sorts of data is erased from the phone. Although this is not one of the most common ways of gathering personal details by an identity thief but this can be seen as an easy target.
Therefore, when you’re eager to avoid all kind of identity thieves and stay safe, you have to take care of the tech advancements and remain aware of how to thwart such things. You can sign up with tech websites which deal with such machines so that you can remain informed.