Cybersecurity professionals are in the business of developing and using as many tools as possible to keep your computer and your wider network safe from attackers. Their work involves analyzing and predicting the behavior of Cyber criminals and developing measures to keep you safe.
Cyber criminals are highly intelligent, and it can be tough to stay one step ahead of them. Browser isolation is a method of Cyber security which means that the attackers behavior does not need to be predicted because any malicious code that might affect your computer never gets anywhere near it.
What are the risks posed by your internet browser
There are a number of risks that are posed to you through your internet browser, which you need to be mindful of every day.
Some of the most common browser security threats are:
- Your browser history. Your browser contains a detailed record of all of your searches and transactions on the internet. This allows criminals to profile you and begin to get an idea of what your patterns are. For example, they might note that you have recently been purchasing a lot of furniture for your new home, so they know that the furniture shop is a good place to go to try and harvest your credit card details. Plus, they know that your credit card company is unlikely to flag transactions there as being suspicious. A good way to mitigate this risk is to regularly clear your cache.
- Harvesting login credentials. If you allow your browser to save your login credentials, some criminals may be able to use this information to their advantage by logging in as you. This can gain them access to your credit card details and any number of personal details – especially on your social media accounts. To mitigate this risk NEVER save your passwords in the browser, instead use a password safe like KeePass or LastPass.
- Autofill information. Autofill information such as your address and other contact details can be harvested by Cyber criminals. A good way to get around this is to regularly clear your cache, and do not allow your browser to save autofill information.
What is browser isolation
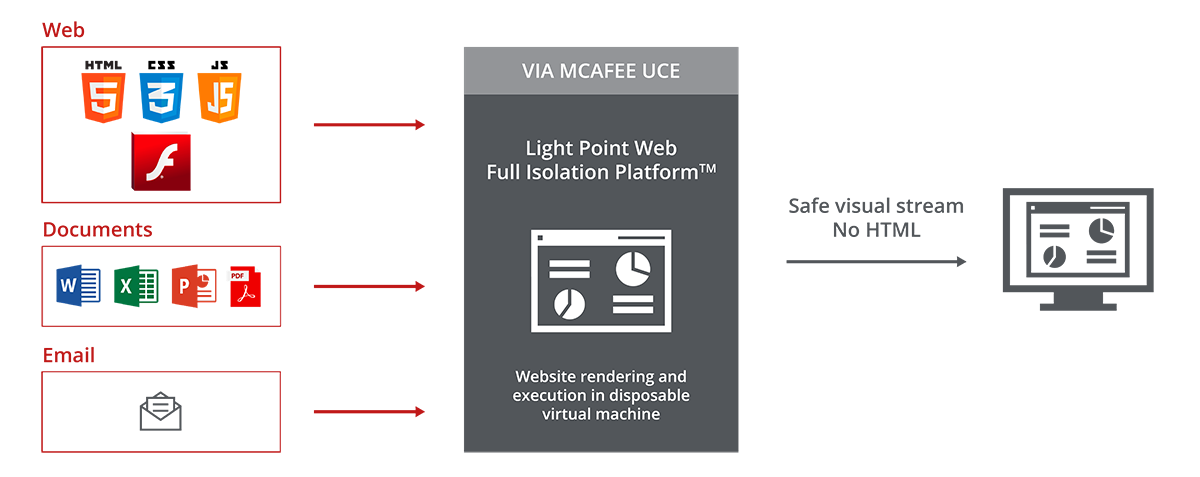
Browser Isolation means that you browse the internet on a virtual browser, which is unconnected to your computer and your network. All that you will see on your computer is harmless pixels.
Because all the code that could potentially harm you is executed away from your computer, the risk of an attack on you is neutralized. This method of Cybersecurity is powerful because it means that there is less emphasis on having to analyze the attackers behavior and predict what they might do. Using the virtual browser simply means that they do not have the opportunity to access any of your information.
It is the equivalent of bolting your door. A burglar can try and pick the lock all they want, but if there is a bolt preventing the door from being opened then they still will not be able to get inside!